StableNet® Network Configuration & Change Management
Reduce configuration errors with vendor independent automation
NCCM at a glance
Configuration standards can be built based on corporate policies, therefore violation of these standards can be mitigated.
The StableNet® NCCM software not only captures every configuration change (Who? What? Where? When?) for a device within its database, but also has the ability to structure large-scale changes into jobs for controlled executions and also roll-back.
At StableNet®, we’ve always designed our NCCM solution with automation at the core. Whether you are using CLI, SNMP, or Netconf, you have a single platform to manage your multi-technology network infrastructure and make sure that every configuration you make is reliable, repeatable, and consistent across your entire network.
Ready to see how StableNet® can transform your network operations and bring you into the future of automated management?
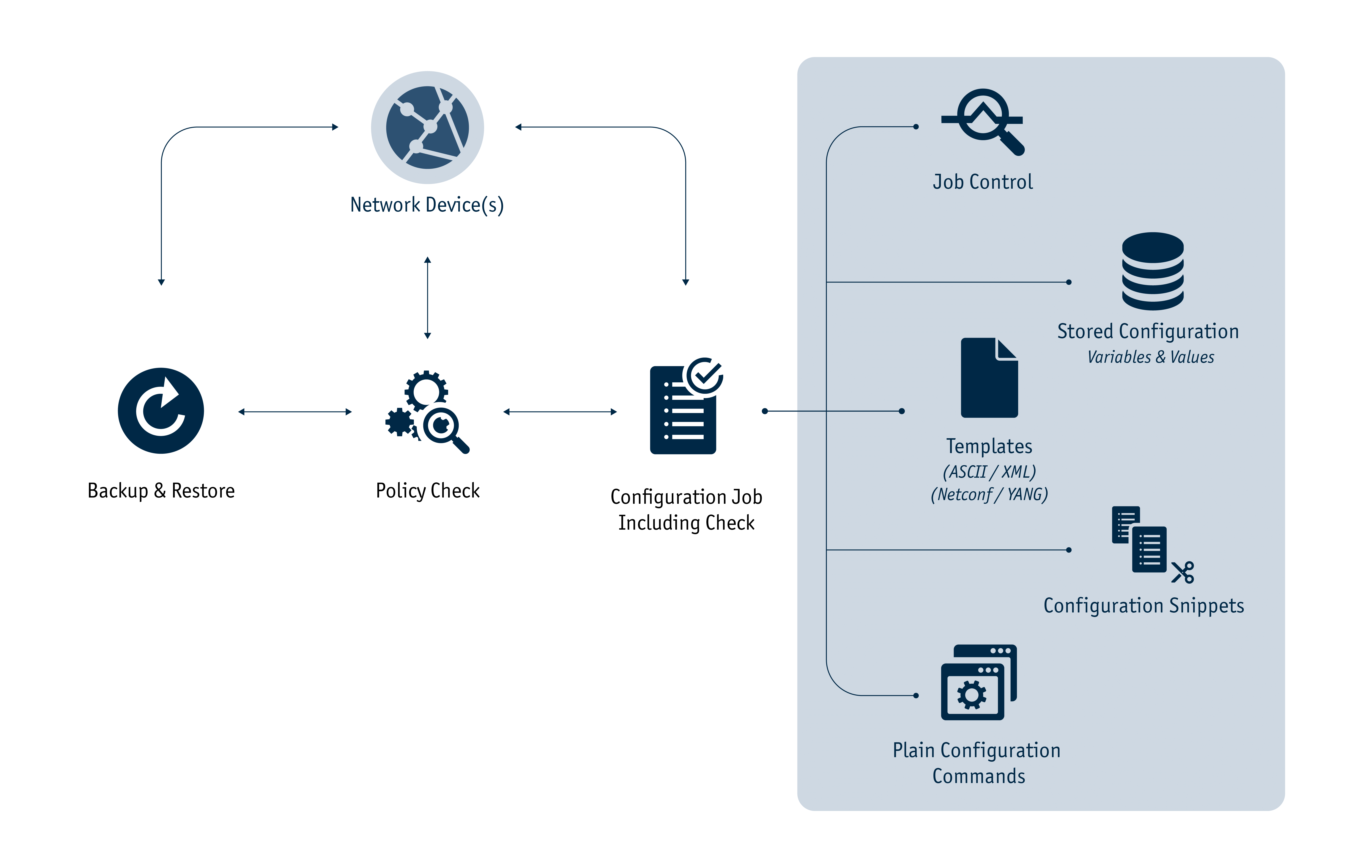
StableNet® NCCM Workflow
Config Generator
StableNet's® easy answer for all your configuration needs
Vulnerability Management
Find and troubleshoot the weaknesses in your network
Lifecycle & EoX Management
An automated, scalable approach to Lifecycle & EoX Management
Policy Management
Policy and Compliance Validation
Zero Touch Provisioning
Fully automated network and services rollout
Configuration
Automation
of complex tasks into simple templates, and therefore accelerating time to complete changes and roll-outs
Elimination of risks
Compliance
Ensuring of compliance with regulatory requirements
Policy management
Enforcing of corporate policies and quickly viewing configuration deviations from those standards
Vulnerability management
Localization of devices within the enterprise that have known vulnerabilities, and mitigation against those risks
ITIL compliance
Enabling the use of best practices within an organization
End-of-Life/End-of-Service
Pro-active identification of devices that have reached EoL/EoS
Use Case: Policy Checking and Compliance
Use Case: Zero Touch Provisioning (ZTP)
NCCM with StableNet® explained on our Youtube Channel: To the Tutorial
Ready for multi-vendor network management?

Software
Made in Germany