Who is communicating with whom in my network?
TUM and Infosim® PoC
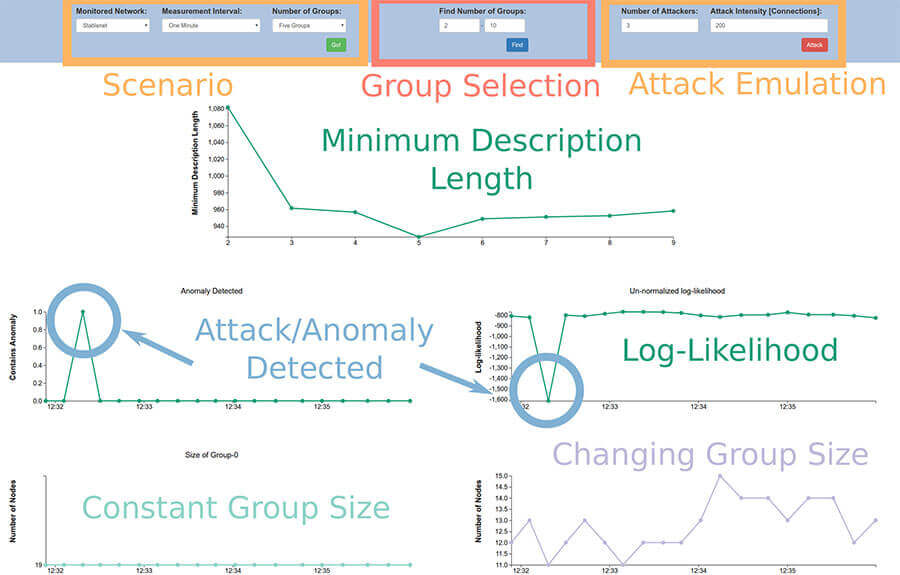
Demonstrated live at SIGCOMM’19 held in Beijing, the PoC showed a system that uses Stochastic Block Models (SBMs) to infer structural roles of hosts and communication patterns of services in networks. The system, called NOracle, can be used with StableNet® to analyze and visualize networks in an online manner or it can be used to analyze stored traces. Network operators can use SBMs to monitor and verify network operation, detect possible security issues and change-points. To showcase this, NOracle combines StableNet® with an SBM based anomaly detection and network visualization module. StableNet® provides network flow statistics in real-time from actual devices. The SBM extracts roles and communication patterns live from the data provided by StableNet®. The result can help to reason about communication behaviors, detect anomalous hosts and indicate changes in the large scale-structure of network communication.
Data is taken live from the enterprise network testbed located at Infosim’s HQ. The enterprise network provides a testbed for trying out network management operations — it consists of more than 100 devices. StableNet® is the core part “glueing” everything together, i.e., it fetches networking data from all devices and makes it available. The demo showed how a network operator can inspect the communication behavior of the users and services live at run-time. Using NOracle’s GUI, a network operator/administrator can investigate the evolution of the network over time, or investigate details of the communication structures within or between groups. Clients that should be blocked from the outside world should not show any communication with “external” groups. In the end, human knowledge is useful or even required to finally infer the semantic meaning of the communication groups.
Want to see more? Look at our Video!
StableNet® & Agentic AI: Introduction & Basic Setup
Learn how StableNet® can be extended with Agentic AI to enable natural language interaction with network data and operations.
The Customer Pilot Hub – A Further Step Towards Open Innovation
With the new StableNet® 26 Annual Release, the Innovation Lab is introducing a new extension: The Customer Pilot Hub.
Getting Started with Data Center Environmental Monitoring
Data center environmental monitoring refers to the monitoring of environmental conditions in a data center, such as temperature and humidity…

Software
Made in Germany