Machine learning assisted monitoring of optical network security
Chalmers University of Technology (Sweden), TIM (Italy), and Infosim® PoC
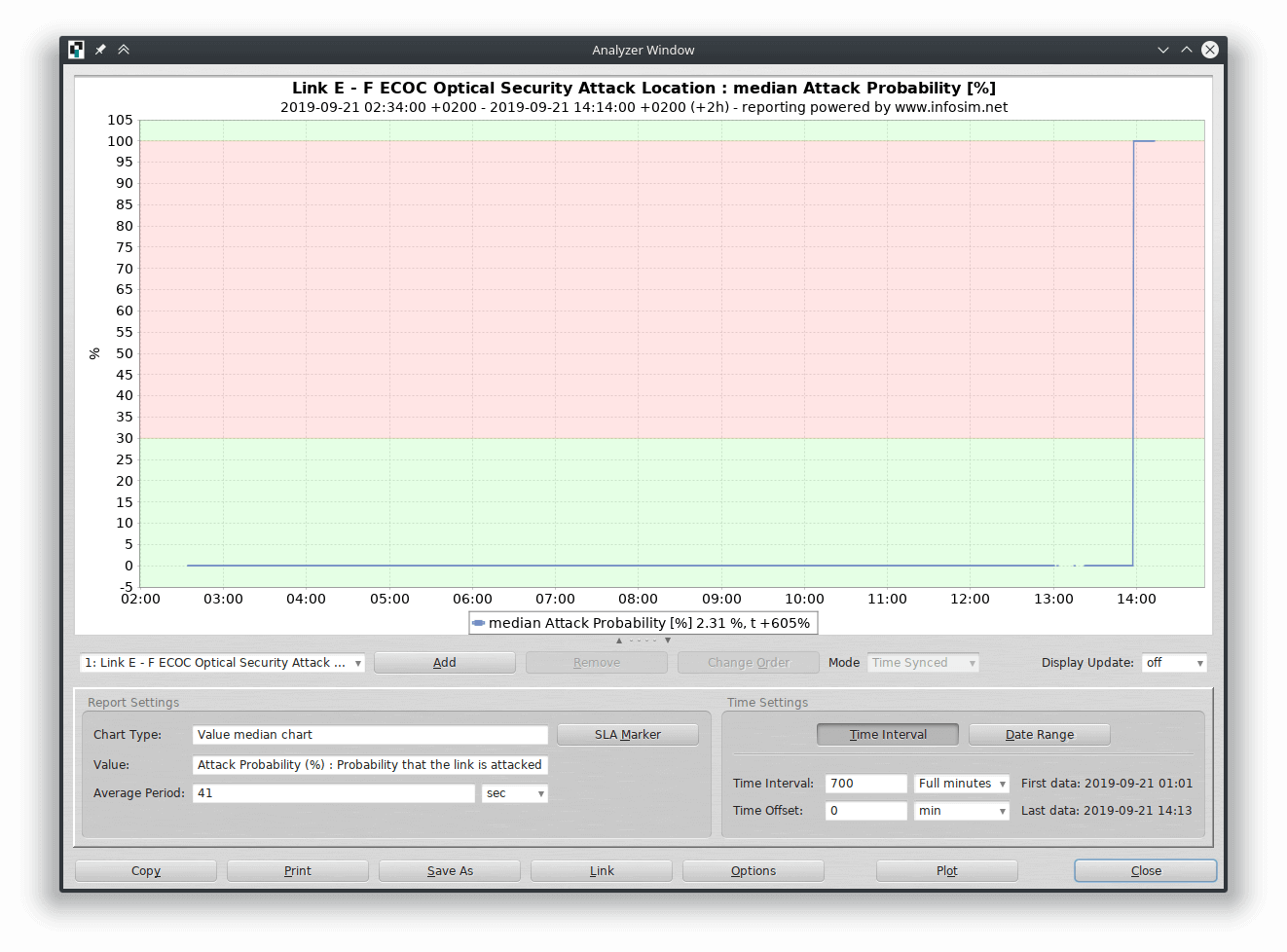
Demonstrated live at ECOC’19 held in Dublin, the PoC showed an integrated approach for detecting and localizing malicious attacks targeting service disruption at the optical layer. The security management system uses the largest experimental data set related to optical network security reported thus far, obtained by subjecting TIM’s network testbed to in-band jamming, out-of-band jamming and polarization scrambling attacks. The data is collected by StableNet® and processed by attack detection and localization modules developed by Chalmers. The type and intensity of an experienced attack is identified by applying a pre-trained artificial neural network, while an unsupervised learning technique DBSCAN facilitates detection of previously unseen attacks. Attack source localization relies on correlating security statuses of connections across the network modelled with binary words called attack syndromes.
The demonstrator features a rich set of attack regimes, where attack type, intensity and physical location can be dynamically selected by the demo attendees through a graphical user interface. The interface also features a rich graphical representation of the outputs of attack detection and localization modules as well as a deep analysis of the security status of each network element. The modules are implemented in the form of containers and use standard, open interfaces, whose interoperability with contemporary network management platforms was showcased through integration with StableNet®. This demonstration represents an important step towards enabling holistic, integrated data analytics and enhancing optical network security.
Want to see more? Look at our Video!
StableNet® & Agentic AI: Introduction & Basic Setup
Learn how StableNet® can be extended with Agentic AI to enable natural language interaction with network data and operations.
The Customer Pilot Hub – A Further Step Towards Open Innovation
With the new StableNet® 26 Annual Release, the Innovation Lab is introducing a new extension: The Customer Pilot Hub.
Getting Started with Data Center Environmental Monitoring
Data center environmental monitoring refers to the monitoring of environmental conditions in a data center, such as temperature and humidity…

Software
Made in Germany